Numerous sites are recently affected by a new type of malware, loaded from cofounderspecials.com. Approx. 160 sites are already indexed by publicwww with this malware.
Try our Free site check.
Follow these steps to recover from this hack:
Linked malicious attack:
https://guides.magefix.com/2022/05/legendarytable-com/
Need help? Let us clean your site.
Malicious subdomains:
spectre.cofounderspecials.com
js.cofounderspecials.com
fly.cofounderspecials.com
Malicious URLs:
https://simple.cofounderspecials.com/tag.js?v=2.00
https://js.cofounderspecials.com/splash.js
https://spectre.cofounderspecials.com/fine.php?pid=4362&tid=68964&cid=555
https://door.cofounderspecials.com/way.php?pid=553246&kid=685&uid=456389&mid=689332
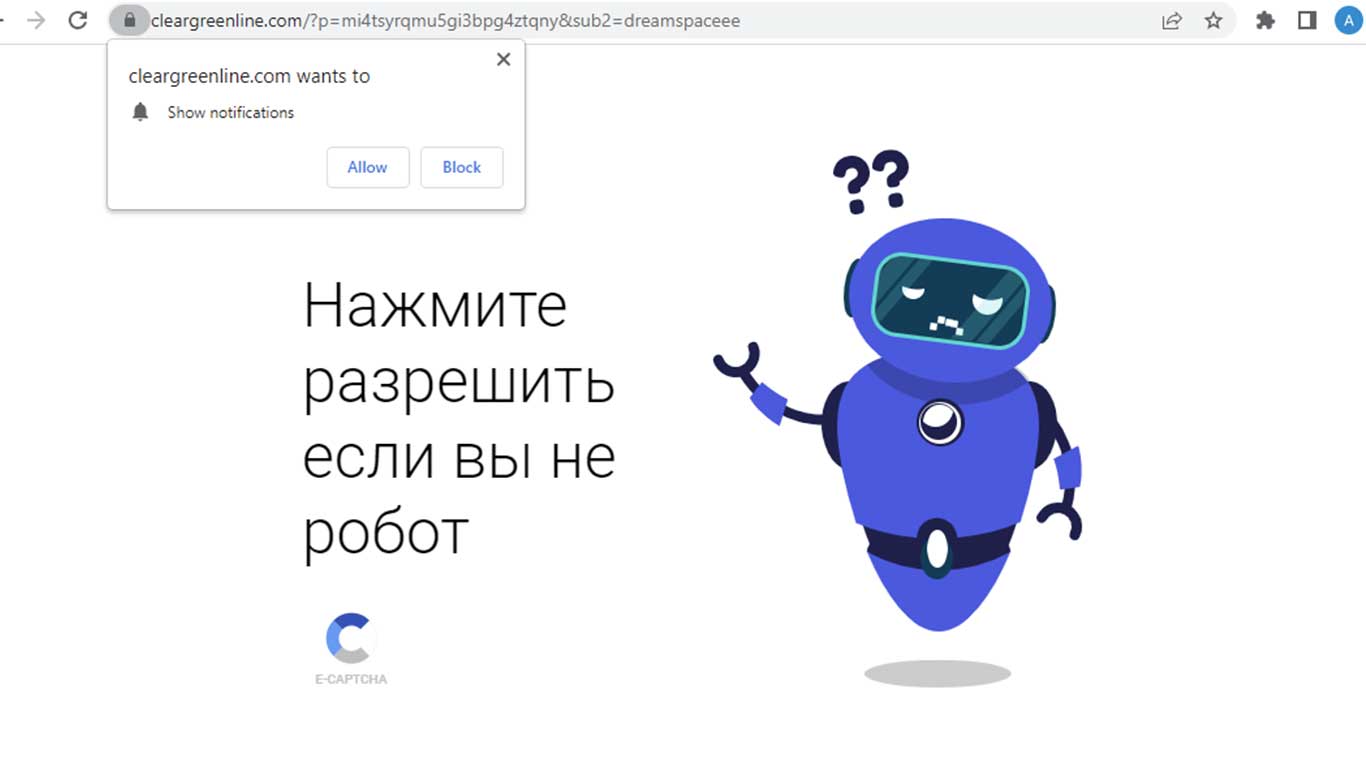
https://cleargreenline.com/?p=mi4tsyrqmu5gi3bpg4ztqny&sub2=dreamspaceee
https://trick.legendarytable.com/news.js?v=9.4.9
https://trick.cofounderspecials.com/way.js?v=0.5.8
https://simple.cofounderspecials.com/
https://clark.cofounderspecials.com
https://scripts.bettershitecolumn.com/sort.js?v=001
https://space.bettershitecolumn.com/cadfl8k.php?key=osyg7q7bz5ig7cma3vc7
https://beat.bettershitecolumn.com/bet.php?id=5478sid=32677&lid=68568
https://away.bettershitecolumn.com/track.php?tid=54889&lid=9554-66-457679-29
https://away.bettershitecolumn.com/hit.php?tid=1311&lid=334-1166-567334-46
Other URLs:
https://goldflowerservice.com/?p=mq2dgm3dgi5gi3bpg42dgna&sub2=Zvold2
https://lingtawatila.ml/help/?23071650902120
http://lukoil-promotion.online/media/mainstream/frame.html
Biz URLs:
https://di5.biz/sw/w1s.js
https://browork3er.cc/sw/bro.js
https://oo00.biz/sw/w1s.js
String.fromCharCode: 104,116,116,112,115,58,47,47,115,112,101,99,116,114,101,46,99,111,102,111,117,110,100,101,114,115,112,101,99,105,97,108,115,46,99,111,109,47,102,105,110,101,46,112,104,112,63,112,105,100,61,52,51,54,50,38,116,105,100,61,54,56,57,54,52,38,99,105,100,61,53,53,53
Malicious IPs:
54.36.118.105, 92.119.160.54, 88.85.94.246 ( Webzilla B.V. ), 101.99.95.147 ( Verdina Ltd. ), 91.211.91.104 ( PE Brezhnev Daniil ), 185.177.94.108, 51.15.15.159, 91.211.91.114 ( PE Brezhnev Daniil ).
Other malicious domains related to this hack:
runholeskin.live, figproax.live, best-prizes-place.life, lukoil-promotion.online, lingtawatila.ml, goldflowerservice.com, goldflowerservice.net, brownluxuryservice.com, rockstonefirst.com, rockstonesecond.com, redstringline.com, cleversmallline.com, duhestyce.com, clearblueline.com, 1.clearblueline.com, cleargreenline.com, 1.cleargreenline.com, di5.biz, oo00.biz.
Twitter update from Denis @unmaskparasites
Another wave of this WP infection campaign: js.cofounderspecials[.]com. https://t.co/S5Ft9guONZ E.g. injections in index.php. Or used in their older scripts.https://t.co/H5SF5F676N pic.twitter.com/nWci7QBIqI
— Denis (@unmaskparasites) July 12, 2022
Subdomains related to this malware attack, that are hosted by the same network, Verdina Ltd.:
refer.specialadves.com
links.drakefollow.com
classicpartnerships.com
print.legendarytable.com
find.greengoplatform.com
javasripts.classicpartnerships.com
brend.specialadves.com
click.specialadves.com
scripts.classicpartnerships.com
ads.specialadves.com
clipjs.legendarytable.com
links.specialadves.com
front.greengoplatform.com
cofounderspecials.com
out.legendarytable.com
js.cofounderspecials.com
flash.greengoplatform.com
specialadves.com
track.transportgoline.com
call.greengoplatform.com
local.drakefollow.com
legendarytable.com
confirmacionsb.com
out.drakefollow.com
local.specialadves.com
dns.classicpartnerships.com
doggy.drakefollow.com
white.classicpartnerships.com
trick.legendarytable.com
javascripts.classicpartnerships.com
sbcomprobacion.com
track.greengoplatform.com
greengoplatform.com
wpn.specialadves.com
drakefollow.com
collect.greengoplatform.com
creative.greengoplatform.com
event.classicpartnerships.com
jack.legendarytable.com
fly.cofounderspecials.com
clip.legendarytable.com
Domains related to this malware attack, that are hosted by the same network, DataWeb Global Group B.V.:
0.lightredstep.com
2.cleargreenline.com
2.gloveryforredwine.com
robot.google.com.to1s.biz
1.gloveryforredwine.com
1.gloveryforbluewine.com
1.cleargreenline.com
sorry.google.com.to1s.biz
gloveryforredwine.com
1.clearblueline.com
1.lightgreenstep.com
2.gloveryforbluewine.com
lightredstep.com
lightgreenstep.com
2.lightredstep.com
google.com.114051130077366335712729.to1s.biz
0.cleargreenline.com
0.lightgreenstep.com
0.gloveryforbluewine.com
0.gloveryforredwine.com
gloveryforbluewine.com
2.lightgreenstep.com
1.lightredstep.com