Since 2021 won’t silence hackers around the world, I’m writing this short guide.
Hopefully it will help website owners to minimise the risk of data loss.
Red flags for compromised sites:
- Domain is blacklisted by Google, McAfee, etc..;
- Corrupted Google search results ( Japanese keyword hack );
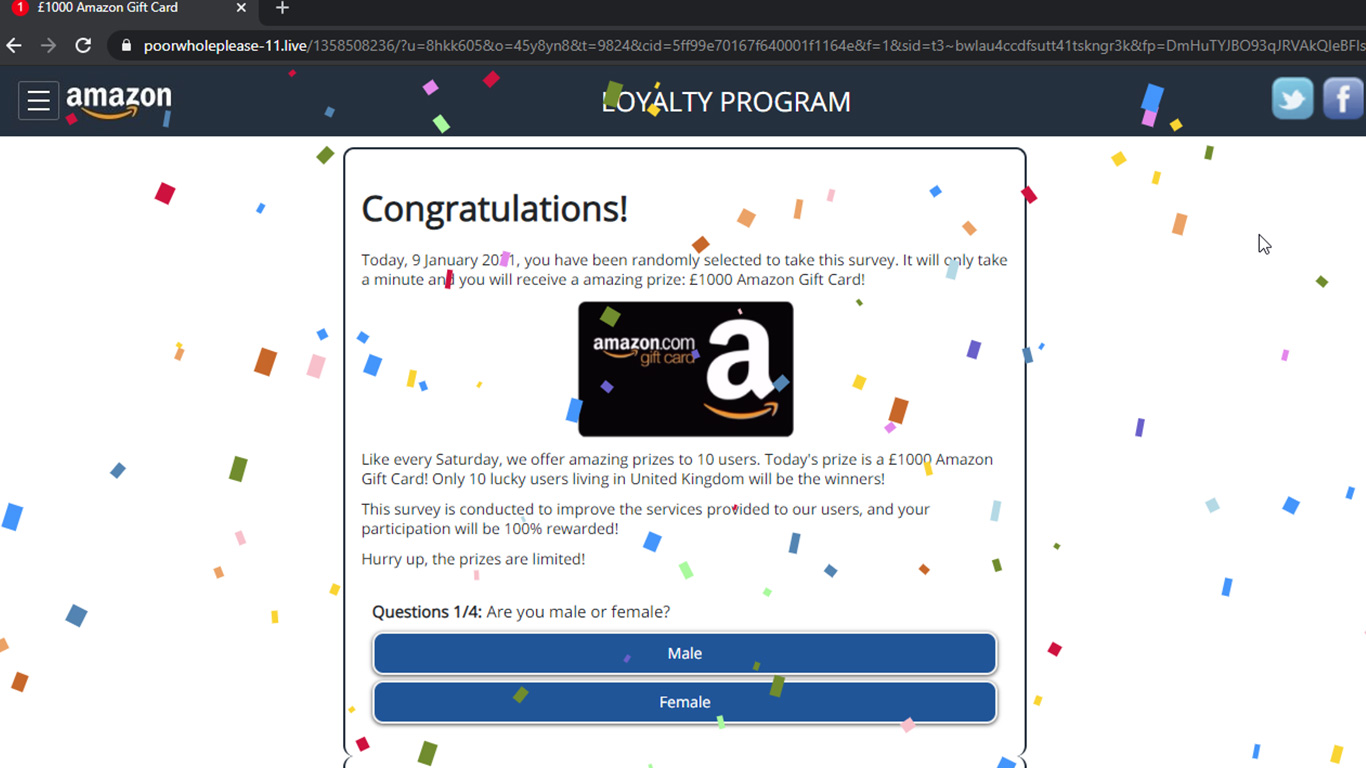
- Malicious random redirects to scam sites;
- Host has disabled your website;
- Readers complaining; and
- You can visibly see that your site has been hacked;
Need help? Let us clean your site.
To secure a hacked website, follow these steps:
2. Replace your index file with a temporary HTML page: https://www.magefix.com/temp/
3. Check if you have other sites are hosted on the same account. If so, cross-site contamination risk is high.
2. Make sure you have several backups available prior to the hack.
3. Secure all the backups on your computer.
2. Disable MySQL remote access, especially if you’re using Plesk.
2. Ask for help:
Wordpress support: https://wordpress.org/support/forum/how-to-and-troubleshooting/
Hacking subreddit : https://www.reddit.com/r/hacking/
3. If you have technical skills, perform the cleanup yourself. A cleanup guide which should work for most WordPress sites can be found here.
Important tips:
1. Don’t rely on automated software, because new malware is build around them.
Example: https://wordpress.org/support/topic/i-see-hacked-code-but-sucuri-says-files-are-all-ok/
2. If you’re using a hosting account managed by Hostgator, BlueHost, JustHost, HostMonster, iPower, iPage or any other EIG web hosting company, avoid their security solutions. Look elsewhere: Magefix, OneHourSiteFix, Sucuri, Upwork, Fiverr.