If your website redirects to ads.specialadves[.]com, most likely your website is hacked.
Moreover, all your site visitors are affected, having their browsers contaminated with adware.
ads.specialadves[.]com may affect both web files and database – make sure both locations are thoroughly checked.
Follow these steps to recover from this hack:
define( 'WP_HOME', 'https://example.com' ); define( 'WP_SITEURL', 'https://example.com' );
Search and replace tools: dnGrep, grepWin, VisualGrep, PowerGREP.
Look for “storerightdesicion”, “specialadves”, and “String.fromCharCode”. Alternatively, you may use your local antivirus to scan the files.
- As a precaution measure, look for “specialadves”, “storerightdesicion” or “String.fromCharCode”. This way you will know if other tables are infected as well.
Injections usually occur in wp_posts and wp_options tables.
Our preferred search and replace database tools for WordPress are Better Search Replace and Search Replace DB. - Check the users with administrator privileges.
Conclusions:
- Always secure a backup before making any changes.
- Thoroughly check the core files, plugins and themes – find and replace the malicious ones.
- Look for malicious backdoors inside /uploads/ folder – preferably disable PHP execution.
- Review the users’ list with admin privileges, FTP accounts, and database tables.
Try our Free site check.
Malicious URLs:
4/26/2022
hxxps://print.legendarytable[.]com/news.js
hxxps://out.drakefollow[.]com/loc2.php
hxxps://out.drakefollow[.]com/out2.php
hxxps://di5[.]biz/sw/w1s.js
hxxps://links.greengoplatform.com/J6KRTp
hxxps://ads.specialadves[.]com/s.php?id=463-24-745783-2
hxxps://ads.specialadves[.]com/go.php?id=123-37-456859-44
hxxps://links.specialadves[.]com/JQnQLm
hxxps://click.specialadves[.]com/c.php?id=883-435852-23-86699434
hxxps://line.storerightdesicion[.]com/ping/?str.js
hxxps://scripts.classicpartnerships[.]com/train.js
hxxps://event.classicpartnerships[.]com/s.php?id=463-24-745783-2
hxxps://event.classicpartnerships[.]com/some.php?id=436&pid=22&sid=4363
hxxps://brend.specialadves[.]com/location.php?spec=8579&p=2285&get=0042
hxxps://local.specialadves[.]com/YWktkM
hxxps://brend.specialadves[.]com/small.php?id=12&sid=7457&pid=6634
hxxps://brend.specialadves[.]com/big.php?id=552&sid=4579&pid=1153
hxxps://local.specialadves[.]com/1QtY8z
hxxps://local.specialadves.com/YWktkM
hxxps://brend.specialadves[.]com/location.php?spec=8579&p=2285&get=0042
hxxps://brend.specialadves[.]com/location.php?spec=2&p=578&get=348
Malicious files: wp-blog-post.php, wp-blockdown.php, wp-blockup.php.
Core files may be also injected and malicious backdoors placed inside the /uploads folder.
Other URLs:
hxxps://refer.specialadves[.]com
hxxps://blame.storerightdesicion[.]com
hxxps://chess.storerightdesicion[.]com
hxxps://vol.belonnanotservice[.]ga
hxxps://get.belonnanotservice[.]ga
hxxps://greendeliver[.]space/bro1.js
hxxps://broworker7[.]com/sw/bro.js
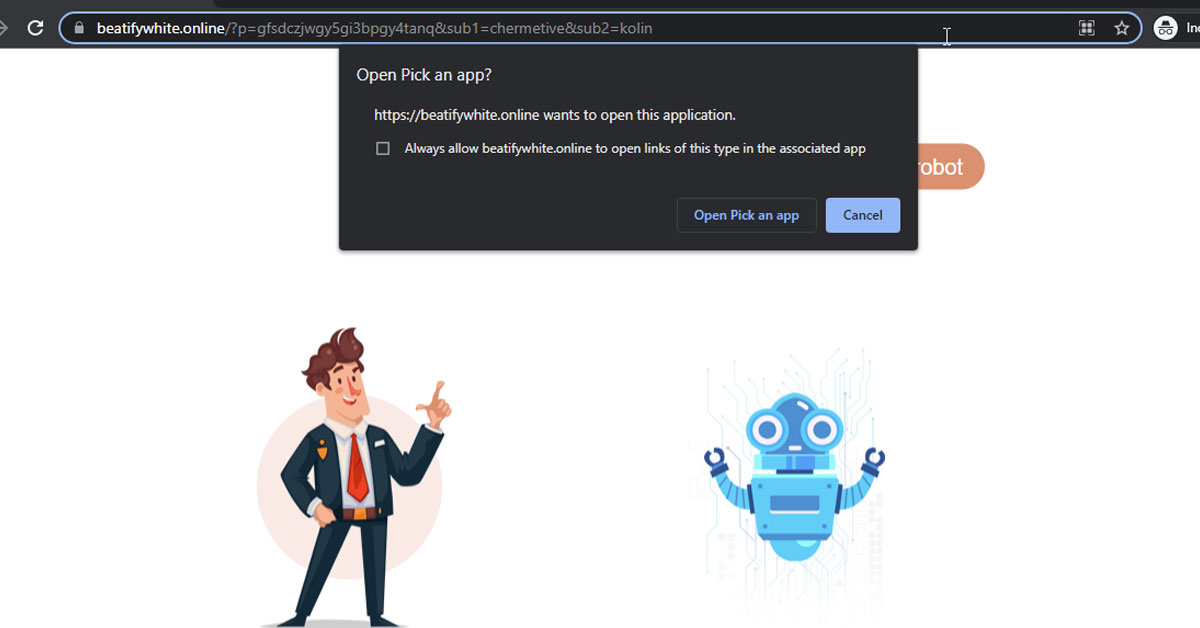
Bad landing pages:
0.flightmachine[.]space/index.php?p=muywey3dmi5dinzyge
0.clockwerkday[.]space/?p=gfsdczjwgy5gi3bpgy4tanq
0.lightformentor[.]space/index.php?p=mvrgkmddmi5demzx
fromCharCode malicious string:
104, 116, 116, 112, 115, 58, 47, 47, 97, 100, 115, 46, 115, 112, 101, 99, 105, 97, 108, 97, 100, 118, 101, 115, 46, 99, 111, 109, 47, 115, 46, 112, 104, 112, 63, 105, 100, 61, 52, 54, 51, 45, 50, 52, 45, 55, 52, 53, 55, 56, 51, 45, 50
Malicious IPs: 45.9.150.78, 104.248.199.158, 212.129.16.248, 188.166.68.96.
ASNs: AS49447, AS12876.
Malicious domain: bollingerjack.online, destinyred.space, 0.crackerthomson[.]tech, 0.clarifyspotify[.]online, clearedspencer[.]top, glickredden[.]tech, classicpartnerships[.]com, specialadves[.]com, storerightdesicion[.]com, storerightdesicion[.]com, belonnanotservice[.]ga, greendeliver[.]space, greendeliver[.]online, 0.velvetking[.]space, beatifywhite[.]space, beatifywhite[.]online, broworker7[.]com, clockwerkday[.]space, fastred[.]biz, di5[.]biz, bigsoul[.]biz, redads[.]biz, se07[.]biz, se19[.]biz, lib1[.]biz, lowrance[.]top, velvetking.space, rosevertical.space, greatvernando.space.
Related guide: https://guides.magefix.com/2022/05/legendarytable-com/.