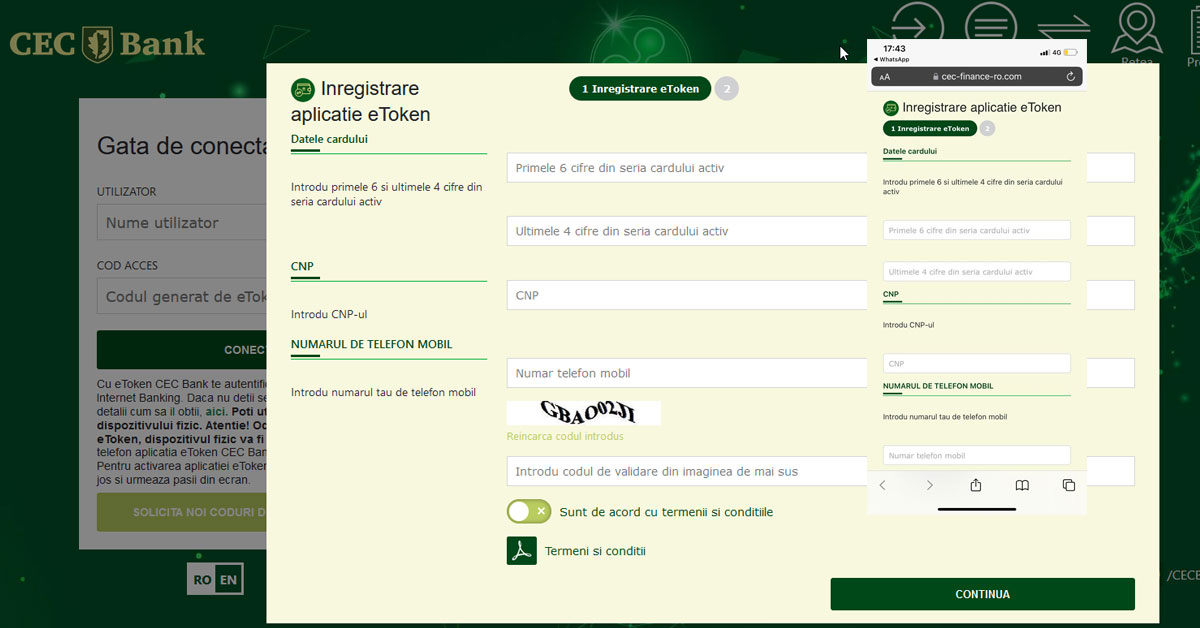
A recent phishing campaign is targeting CEC BANK customers from Romania. The attackers exploit the weebly.com network and then use a bridge site that directs the users to the malicious landing page where the data is collected.
Several examples of malicious links:
Step 1. The first link which is inserted in the phishing email campaign: http://click.promote.weebly.com/ls/click?upn=
Step 2. formaveneto.it/ughgyf or ceaproma.it/gbwhshd , IPs: 89.46.109.40, 89.46.109.24 ( AS31034, Aruba )
Step 3. cec-finance-ro.eu/cec/ or cec-finance-ro.com/cec/, IPs: 62.149.128.45, 62.149.128.40 ( AS31034, Aruba )
Malicious URLs:
https://www.cec-finance-ro.eu/cec/auth/login.php
https://www.cec-finance-ro.com/cec/auth/login.php
https://wwww.zetar.it/cec/ 62.149.128.154 ( AS31034, Aruba )
https://app.fnaemiliaromagna.it/ign/home/auth/login.php
https://ceconline-ro.com/auth/login.php
Phishing email headers
Received: from 167.89.26.247 (EHLO o5.promote.weebly.com)
Received-SPF: pass (domain of promote.weebly.com designates 167.89.26.247 as permitted sender)
Phishing URLs are deceptive websites designed to steal your personal information, such as personal data and bank details. Recognizing phishing URLs is very important – here are some tips to help you identify a phishing campaign:
- Use a good antivirus, on both PC and phone. We recommend ESET, and McAfee – every time we report malicious URLs, they promptly reply and update their database.
- If you suspect a phishing attempt, report it to the relevant authorities or the organization being impersonated. Report the phishing URL to: Google, Netcraft, ESET.
Also, if your website was exploited in a phishing campaign, we can help you to recover from it.
MAGEFIX SecurityMalware cleanup & blacklist removal
Try our Free site check.