Another wave of hacks is ongoing, this time under declarebusinessgroup.ga.
A cleanup guide is available here: https://guides.magefix.com/2020/08/go-donatelloflowfirstly-ga/
Need help? Let us clean your site.
Important – If your not a tech person with WordPress knowledge, then simply:
a) ask us or contact a web security expert to handle the situation; and
b) contact your web host and ask them to move your web files outside public access, to prevent data loss;
Site files cleanup notes
Almost all web folders will get infected, so it will be wise to start fresh 100%.
1. Perform overall backup – site files and database;
2. Move all web files outside root folder, to prevent further data loss;
3. Rebuild everything making sure plugins, themes are all malware free;
4. Restore wp-config.php and wp-content/uploads folder, but make sure these are malware free ( manual check ); and
5. Make sure core files, plugins and theme are up-to-date ( delete everything unused or abandoned );
Database cleanup
1. Use phpMyAdmin and look for “fromCharCode”, “lowerbeforwarden” and “declarebusinessgroup”;
2. Use a search and replace tool, to get rid of malicious entries:
https://wordpress.org/plugins/better-search-replace/
https://interconnectit.com/products/search-and-replace-for-wordpress-databases/
3. Make sure no extra admin users were added by hackers;
Malicious URLs:
hxxps://bono.declarebusinessgroup.ga/m.js
hxxp://mfa.declarebusinessgroup.ga/det.php
hxxps://solo.declarebusinessgroup.ga
hxxps://mono.declarebusinessgroup.ga
hxxps://mono.declarebusinessgroup.ga/det.php
hxxps://sinistermousemove.art/w_14.js
hxxps://url-partners.g2afse.com/click?pid=9824
hxxps://save.declarebusinessgroup.ga/locate.html
hxxps://save.declarebusinessgroup.ga/forward.html
hxxps://solo.declarebusinessgroup.ga/temp.js?n=ns1
hxxps://back.declarebusinessgroup.ga/call.php?id=985-34-332-57
hxxps://sinistermousemove.art/?p=gfqtqojrmu5gi3bpgiydknq
hxxps://0.sinistermousemove.art/?p=gfqtqojrmu5gi3bpgiydknq
hxxps://2.sinistermousemove.art/w_14.js
hxxps://trendopportunityfollow.ga
hxxps://0.trendopportunityfollow.ga/w_29.js
hxxps://net06.biz/sw/w1s.js
hxxps://sunsetregistered.art/w_15.js
hxxps://allowandgo.club/sw/w_11.js
String.fromCharCode: 104,116,116,112,115,58,47,47,98,97,99,107,46,100,101,99,108,97,114,101,98,117,115,105,110,101,115,115,103,114,111,117,112,46,103,97,47,99,97,108,108,46,112,104,112,63,105,100,61,57,56,53,45,51,52,45,51,51,50,45,53,55
>> back.declarebusinessgroup.ga/call.php?id=985-34-332-57
104,116,116,112,115,58,47,47,115,111,108,111,46,100,101,99,108,97,114,101,98,117,115,105,110,101,115,115,103,114,111,117,112,46,103,97,47,116,101,109,112,46,106,115
>> solo.declarebusinessgroup.ga/temp.js
This is clearly related to the previous attacks, temp.lowerbeforwarden.ml.
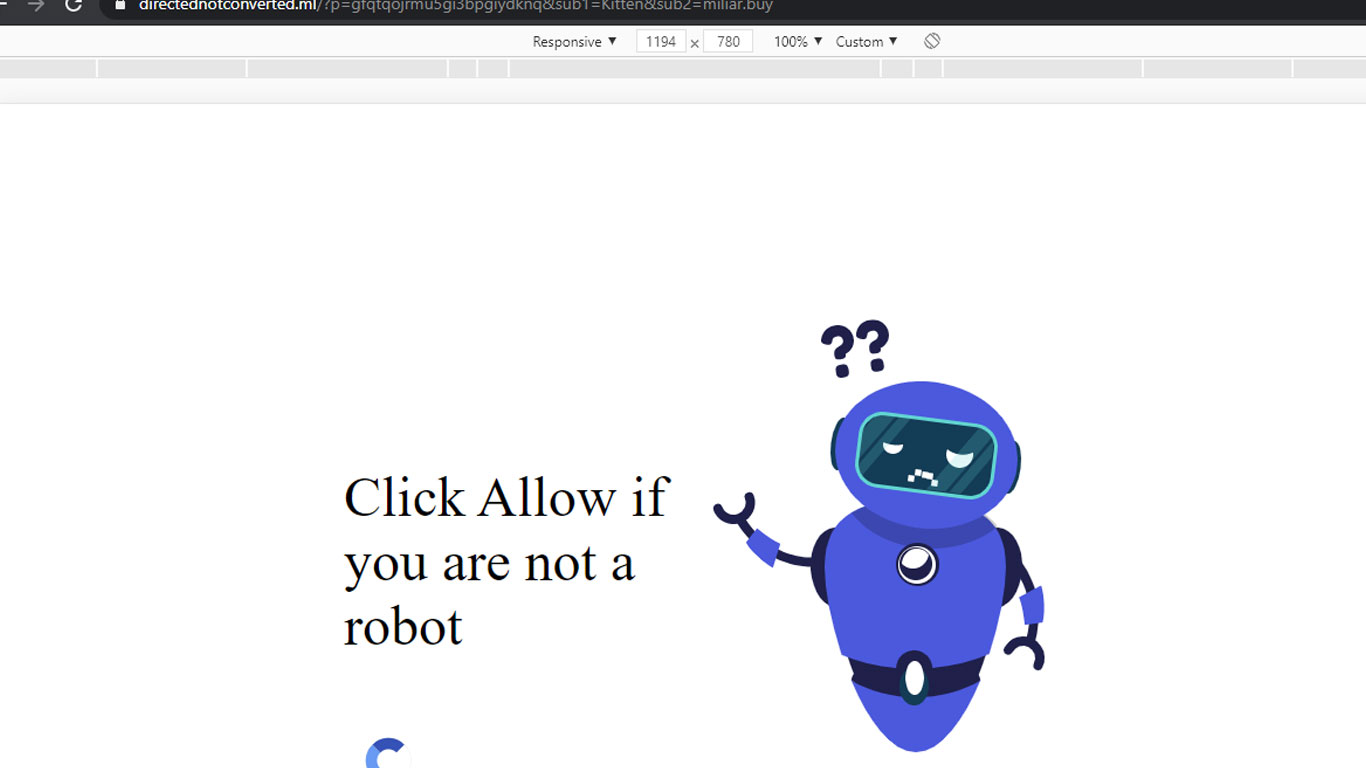
Malware behavior: Vulnerable WordPress sites, with File Manager plugin activated, are injected with malicious scripts hosted by declarebusinessgroup.ga. When a users visits an infected website, browser gets redirected to either: sinistermousemove.art, check-you-robot.site, mobile-global-apps-store.life, check-you-robot.online, vildq.com or any other landing page hosted by 157.245.79.75.
How contamination occurs:
a) First attacker search and exploit a vulnerable file.
198.27.81.188 – – [07/Sep/2020:04:52:01 +0200] “POST /wp-content/plugins/wp-file-manager/lib/php/connector.minimal.php
192.95.30.59 – – [11/Sep/2020:12:49:06 +0200] “POST /wp-content/plugins/wp-file-manager/lib/php/connector.minimal.php
b) Once the first malicious file is being generated, malware spreads.
198.27.81.188 – – [07/Sep/2020:04:53:38 +0200] “GET /wp-content/plugins/wp-file-manager/lib/files/xxx.php
192.95.30.59 – – [11/Sep/2020:12:49:26 +0200] “GET /wp-content/plugins/wp-file-manager/lib/files/x.php?cmd=whoami
Domain details: According to domaintools, domain was registered on 9/9/2020 and it’s pointing to:
Main IP address, 45.9.148.228 – is part of a larger network called “Nice IT Services Group Inc.“.
Try our Free site check.
solo.declarebusinessgroup[.]ga malware injections in wp_posts and in index.php files (not limited to these). Again the same ongoing WP attack that exploits multiple plugin and theme vulnerabilities pic.twitter.com/MrwIHLb6Ls
— Denis (@unmaskparasites) September 9, 2020